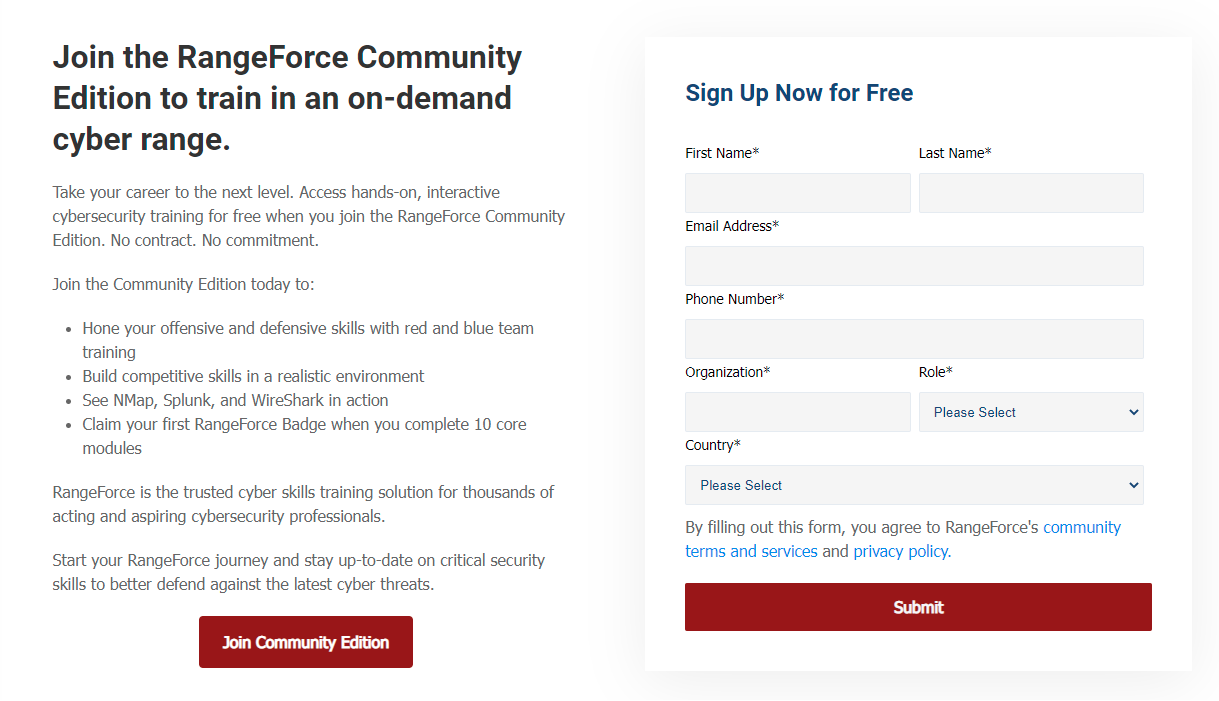
The MIRTE D3FEND Knowledge Graph lists common cybersecurity countermeasures. (Full size photo)
On June 22, 2021, the National Security Agency Cybersecurity division released details of a new project called D3FEND. “D3FEND, a MITRE research project funded by the NSA, improves the #cybersecurity of NSS, DoD, and the DIB by providing defensive countermeasures for common offensive techniques” (NSA Cyber, Twitter).
The MITRE Corporation is a federally funded organization that supports cybersecurity research and development. To better understand this D3FEND release, it is helpful to know about MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge), which was first developed in 2013. “The MITRE ATT&CK framework is a curated knowledge base and model for cyber adversary behavior, reflecting the various phases of an adversary's attack lifecycle and the platforms they are known to target” (McAfee, 2020). This framework allows individuals and organizations to better understand the tactics and techniques used by malicious attackers, and to better prepare for and defend against those attacks.
The 2021 release of MITRE D3FEND is a major tool that blue teams can use to protect against exploitation. This framework will allow cybersecurity professionals to fill the gaps in their coverage, comparing their current setup to the D3FEND framework. “These initial results show good promise, and we believe our research has demonstrated the feasibility of a countermeasure model built from real-world data sources” (MITRE, 2021).
For more information, check out the technical whitepaper released by MITRE here.