The OWASP Top 10 is a list of critical security vulnerabilities for web applications. OWASP stands for the Open Web Application Security Project, which is a nonprofit foundation dedicated to improving the security of software. The OWASP Top Ten list is updated every several years to reflect the changing cybersecurity landscape and to direct focus onto the most important current security issues. The OWASP Top Ten for 2021 is as follows:
A01:2021-Broken Access Control allows an attacker to gain access to user accounts. The attacker in this context can function as a user or even an administrator of the system. This can be secured by ensuring that all accounts use the principle of least privilege and unused accounts are disabled immediately.
A02:2021-Cryptographic Failures occur when important stored or transmitted data is compromised. This vulnerability is also known as “Sensitive Data Exposure.” This can be improved by properly encrypting data at rest as well as data in transit.
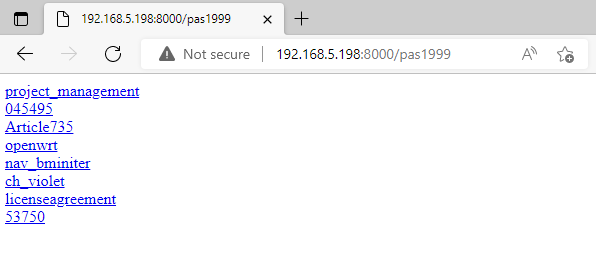
A03:2021-Injection, or more specifically “Code Injection,” occurs when invalid data is sent by an attacker into a web application in order to make the app do something it was not designed to do. Writing secure code that is resistant to input fuzzing can help secure against this type of vulnerability.
A04:2021-Insecure Design is a generic term for web application vulnerabilities that are related to design flaws. Improvements in this category require the use of threat modeling, secure design patterns and principles, and reference architectures.
A05:2021-Security Misconfiguration describes design or configuration weaknesses that are the result of errors or shortcomings. Proper development and quality assurance testing will help secure against misconfigurations.
A06:2021-Vulnerable and Outdated Components relates to devices with known vulnerabilities that need to be patched. If a device or piece of software cannot be patched, it should be removed or replaced with a more secure option.
A07:2021-Identification and Authentication Failures leads to compromised passwords, keywords, and sessions which can translate to stolen user identity. This can be secured through proper user authentication and session management, as well as user education regarding password hygiene.
A08:2021-Software and Data Integrity Failures can occur when software updates or critical data is used without verifying integrity. This can be improved through hashing techniques to verify data accuracy and integrity.
A09:2021-Security Logging and Monitoring Failures are common when logging is not performed frequently and consistently. This type of failure can result in data exfiltration and other attacks.
A10:2021-Server-Side Request Forgery happens when a web application fetches a remote resource without validation, which can give an attacker access to critical data regardless of firewalls or other defensive tools. Proper validation is required to protect against this threat.
For more information about each vulnerability and how to defend against these attacks, check out the OWASP Top Ten website. Thanks for reading - check out my YouTube channel for more!